
Twitter cryptocurrency scams: A hundred Elon Musks — and now Target
Twitter cryptocurrency scams are becoming more and more advanced and convincing, with scammers using new techniques and some heavy artillery.
446 articles

Twitter cryptocurrency scams are becoming more and more advanced and convincing, with scammers using new techniques and some heavy artillery.

We explain the types of malware that can take control of your device, and the dangers of multifunctional infection.

One short message is enough to send a Sony PS4 into an infinite restart loop. Here’s how to deal with it.

Android lets you configure app permissions to protect your data and restrict access to dangerous functions. We explain how to do it and why.

Let’s talk about mobile malware that can empty your bank account or spy on you.

Fortnite for Android is not available on Google Play. We explain how to download and install it properly, and what else to do to stay safe.

How a seemingly harmless Android application can infect your smartphone using shared external storage.

The infamous Lazarus group’s newest campaign is really hard to detect. Bonus: How cryptocurrencies, cybercriminals, and ramen noodles are connected.

Instagram hacking has been on the rise lately. Here’s what you need to know to avoid losing your precious account.

Almost half of the most-visited websites open visitors to potential dangers. What can you do?

KeyPass ransomware is infecting computers worldwide, encrypting almost everything in its path. And it all starts with downloading a seemingly innocuous installer.

Take a stroll through your apps and you’re bound to encounter some unfamiliar names. Where do those unaccounted-for apps on your PC come from, and are they safe?

How a sculpture from Japan is scaring WhatsApp users around the world, and how to protect children from such spooks on the Internet.

In this part, we consider mobile malware capable of causing real damage to smartphone and tablet users.

More than 400 manufacturing companies became phishing targets.

When I fell victim to sleight of hand and a little bit of fraud, Find My iPhone didn’t save me. Here’s why.

Fileless malware infects workstations and servers in corporate networks.

In this edition, Jeff and Dave discuss how a McDonald’s drive-thru was hacked, USB drama, and more.

The Rakhni encrypting ransomware, known since 2013, is now trying its hand at mining Monero.
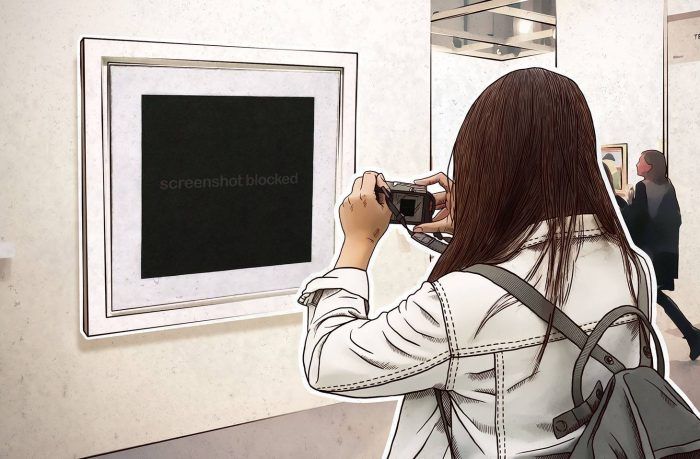
It’s not Malevich’s Black Square. This is what a screenshot taken by a suspicious application on a computer protected by Kaspersky Lab products looks like.

No PIN on your phone? Pickpockets will thank you for that.