
A photo editor with a difference
How a photo editor app from Google Play secretly signed up users for unwanted paid services.
446 articles

How a photo editor app from Google Play secretly signed up users for unwanted paid services.

What the Hoax verdict means, and why such software is becoming more of a problem.

A new spam mailing threatens the reputations of small businesses websites.
Scammers are using Google Calendar, Photos, Drive, and other services to distribute spam. Here’s how it works.

Scammers posing as CIA agents demand ransom for alleged possession of child porn, threatening arrest.
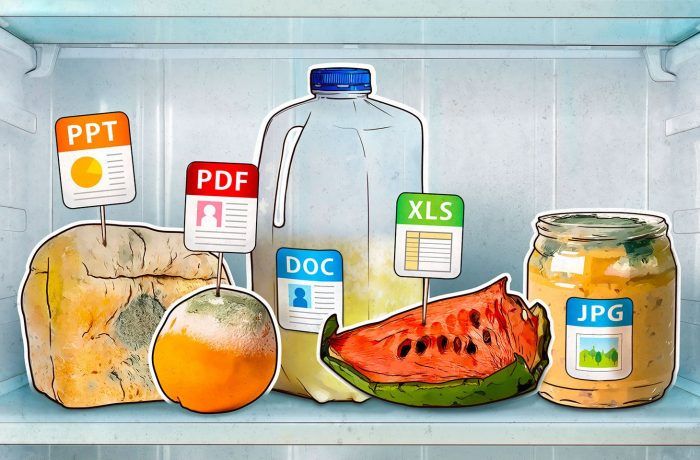
Three real-world examples to illustrate the dangers of digital clutter.

Malware is often distributed in files disguised as episodes of popular TV series. We talk about the most dangerous TV series and how to spot the threat.

A close look at Pirate Matryoshka malware, and why even inveterate pirates should not download cracked software from torrent trackers.


Can an ATM turn into a slot machine? WinPot malware helps its owners win big at the “ATM game.”

The story of a guy who just wanted to download a pirated copy of a game but got malware instead. It’s happening more and more often, and we explain why.

We explain how ultrasound and audio recordings hidden in background noise can be used to control voice assistants.

Changing passwords regularly is outdated. Use strong and unique passwords that are easy to remember instead. Here’s how to make them.
Experts discovered lots of interesting things in the code of North Korean antivirus SiliVaccine.
They say they have video of you watching porn, threaten to send it to your friends, and demand ransom in bitcoins? Don’t pay! We explain how this scam works.

Why you shouldn’t open messages with e-cards from strangers, or believe that someone gave you an Amazon gift card for Christmas.

In this episode, Jeff sits down with Vicente Diaz of Kaspersky Lab’s GReAT to discuss a review of APTs in 2018 and what 2019 may hold.

The 5 most common ways spammers can trick you into paying them or giving up your personal information.

Malefactors do not need to infect your computers with malware if they can just plug their devices right into your network.

We take a look at the Rotexy mobile Trojan: where it comes from, how it behaves, and how to get rid of it using a couple of regular SMS.

The winter sales season is the hottest time of the year for shoppers and financial phishers. Be careful!