News websites often feature stories about computer errors and vulnerabilities used to perpetrate sophisticated large-scale incidents like last year’s WannaCry and NotPetya attacks. But experts know that most successful hacks and cracks are the result of very basic blunders by system developers or installers.
Incorrectly configured systems are everywhere, and only a few hours separate the moment when a hacker first sniffs out such a system and its total surrender to the human intellect. Speaking at the Security Analyst Summit 2018, Israeli researcher Inbar Raz gave a host of examples confirming this sad fact.
Free coffee
Many coffee shop loyalty cards work as follows: the customer receives a card, tops it up like a bank card, and then uses it to pay in the café, earning bonuses for large or frequent purchases. The customer can check the balance on the coffee chain’s website by entering the card number.
Having got hold of such a card for himself, Inbar Raz noted that the website lets users check cards with any number as many times as they like. So, using a tiny program that took him half an hour to write, Raz went through a bunch of different card numbers and identified ones that were topped up with plenty of cash.
Next, after reading the magnetic strip of his card with a cheap USB reader, Raz found that the number had been written to the card in unencrypted form, and the only security was a control bit that was quite easy to compute. The task of replacing the number on the card’s mag stripe with one of the numbers found in the previous step and using someone else’s funds was child’s play.
Ethically minded, Raz proved the concept in practice by buying another card, topping it up, and writing its number to the first card. It worked. In theory, an eagle-eyed café employee could still spot the deception by comparing the number printed on the card with the one on the receipt. But in practice, that ain’t gonna happen. So, it’s basically unlimited free coffee for the hacker — and perhaps a muffin for good measure.
Uber-style tracking
A while back, Uber was hit by a scandal involving claims that employees had misused the mobile app to track high-profile passengers.
It turns out that other taxi services let you do it without the hassle of having to work for them. Inbar Raz discovered that when a taxi is booked online, its status can be tracked using the contact phone number — and as in the free coffee case, there is no protection against brute-force searches.
He wrote a small number-busting program and ended up with a handy map indicating the addresses of all recent taxi orders for this service.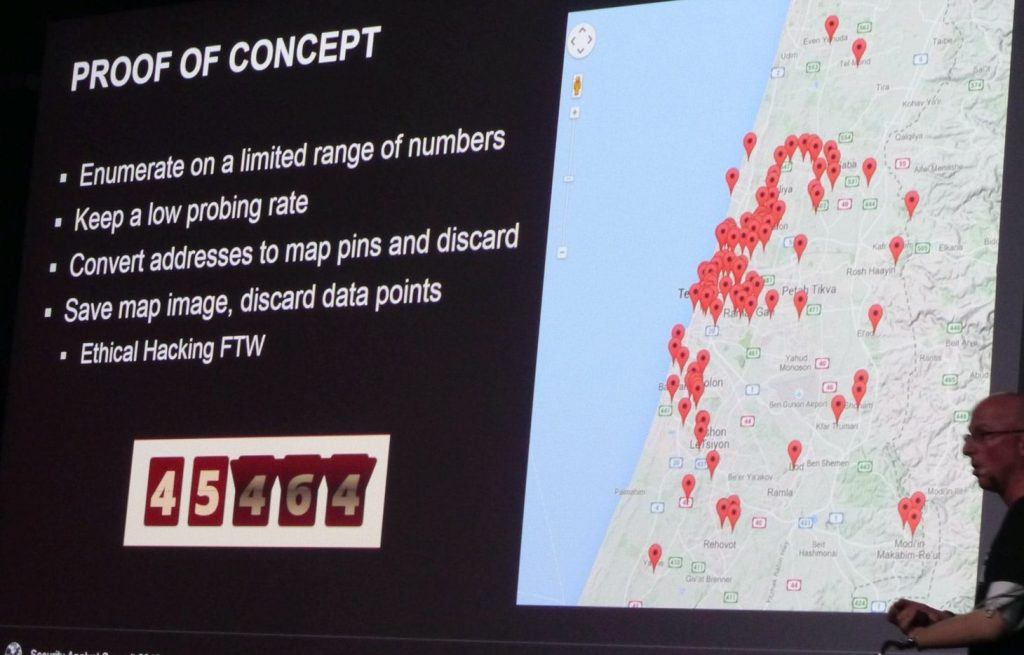
Airport (in)security
Standard free Wi-Fi sometimes harbors hidden surprises. In the business lounge of one East European airport, Inbar Raz decided to check out the configuration of the local access point.
The router settings, he found, could be opened at the standard Web address with no need for an administrator password. Having studied the settings, Raz realized it wasn’t simply a guest access point, but the airport’s main router with vital dispatch and security systems hooked up to it. These services could be disabled by anyone with a laptop or even a smartphone.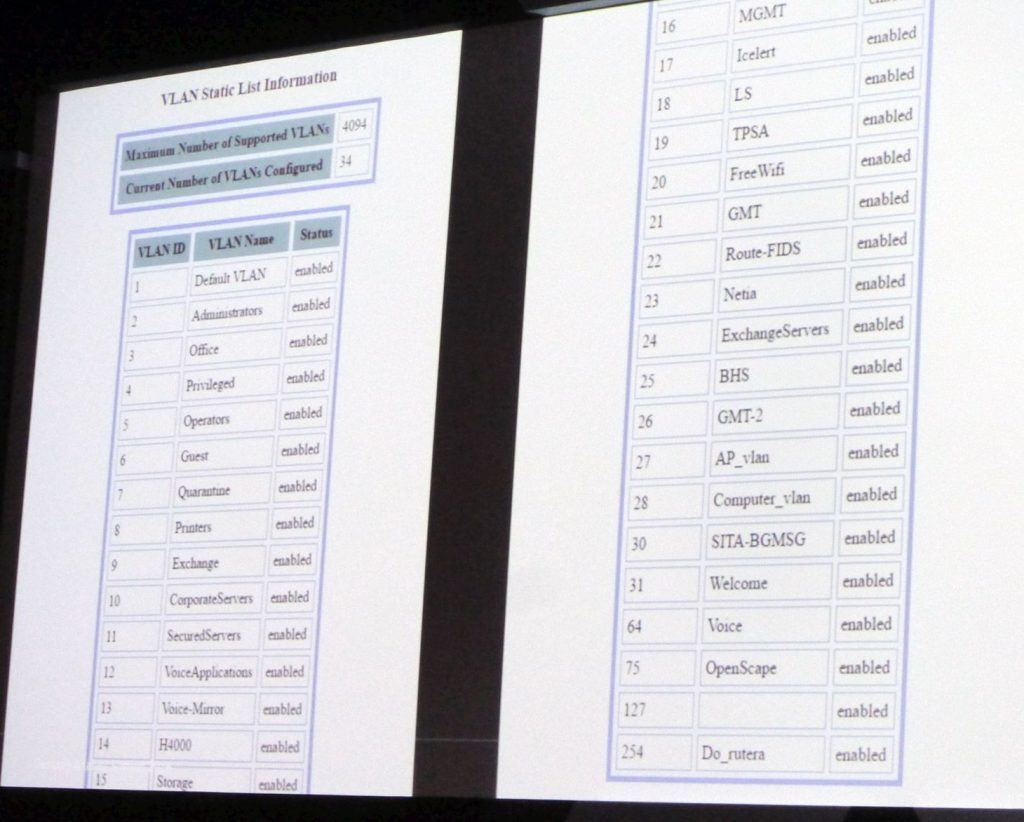
Programmers and system administrators, take heed. Don’t assume that your little café (or taxi service, or airport) is too niche for hackers. Standard settings, simple passwords like “admin” or “12345,” and no CAPTCHA or other measures against automated attacks are the most common security faux pas, and the simplest way in for intruders. Even lowly hackers can exploit them. And guys like Inbar Raz — people who responsibly disclose vulnerabilities to you instead of exploiting them for their own profit — are few and far between.
 SAS
SAS

 Tips
Tips