
Blackphone review: is a secure smartphone possible?
We have bought our very own Blackphone to check its security firsthand.
1447 articles

We have bought our very own Blackphone to check its security firsthand.

A recap of last week’s security news and research from the Black Hat hacker conference in Las Vegas, Nevada.
Unpatched flaws in Android make your device vulnerable to “Invisible” infection. You better find out now in order to protect yourself.

Some things we routinely do in the office are dangerous for careers as they pose significant risk to the company’s business. It’s equally relevant for CEO and intern alike, so watch out!

Yahoo plans to implement end-to-end encryption for all of its mail users, giving normal, non-technical users the power to communicate securely and privately.
Car hacking is back and Charlie Miller and Chris Valasek no longer have to plug their computers into the cars to make them do their bidding.

Data breaches have become a routine. It can happen to any site, any day. You can’t prevent it, but there is a way to minimize the damage.

July is over and that means it’s time to look back and observe the latest results of the battle between cybercriminals and prosecutors.

In the news this week: more APT campaigns, a look forward at the DEF CON and Black Hat Hacker conferences, and good and bad news for Facebook.

In the news: Microsoft’s No-IP takedown fiasco, Chinese APT groups curious about U.S. Iraq policy, Verizon says the government wants locations data, and Microsoft denies backdoor insinuations.

Your iPhone runs hidden monitoring services. Who uses them, and for what purpose?

Facebook fails to fully encrypt data on its Instagram mobile app, which puts user security and privacy at risk.

School’s out for summer and the kids need watching. Here are some tools that can help you do the job – at least while they’re on the Internet.

If it is absolutely necessary that you check your email and the only way to do it is on a public computer, forward your email to a disposable email account like Mailinotor or Trashmail that has a short life and a timed expiration.
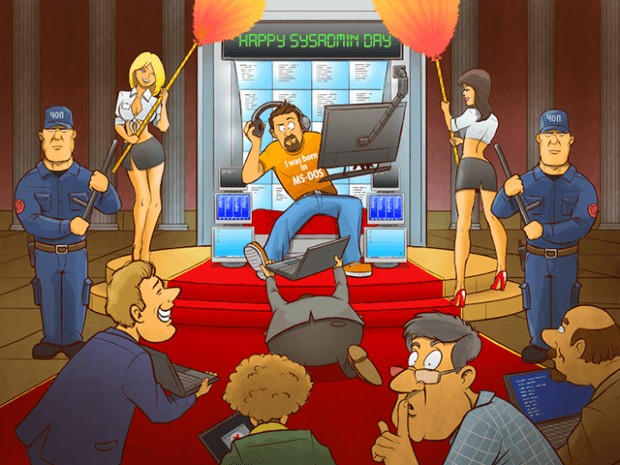
Know your sysadmin and what to expect from him. Don’t forget to congratulate the guy, today is Global Sysadmin day!
A new version of file-encrypting malware hides its sever inside an anonymous TOR network, making it safer for criminals to extort money from victims.

Most free apps are not actually free. They monetize on displaying ads to you ― and sometimes it is very annoying.
Igor Soumenkov, a Kaspersky Lab contributor to the Ubisoft’s Watch Dogs script assessment, explains how close to real life the game world is.

Making a case for password reuse, Google hiring hackers to fix the Internet, Apple bolsters security across its services with strong Crypto, plus various fixes and more.
Any new technology can be rough around the edges. The consequences can be complex and there’s high chance for human error, especially when it comes to security.