
Internal threats: “accidental sharing” leads to loss of more data than software flaws
Internal and external threats may be quite different in nature, but they demand equal attention from the IT staff in order for the protection to be complete.

Musician and technology enthusiast.
356 articles

Internal and external threats may be quite different in nature, but they demand equal attention from the IT staff in order for the protection to be complete.

We’re taking a look at the security features in the new version of Mac OS X – Yosemite. Apple makes a decent effort.
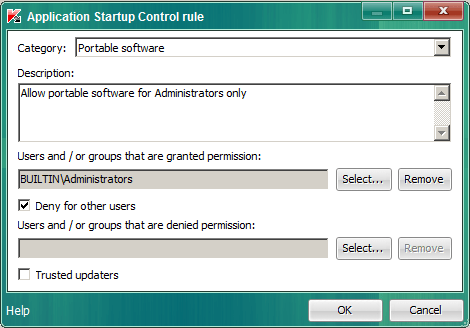
Kaspersky Lab has launched public beta-testing of its enterprise security solution, Kaspersky Endpoint Security 10 Service Pack 1. Take a look at the screenshots showcasing the new features.

Hotels offer not just free WiFi but occasionally even free use of devices such as iPads these days. While it is really nice, a misconfigured device like this may store just a bit too much personal data, easily retrievable by the next visitor…
Every fifth Android-based device protected by Kaspersky Lab security solutions was attacked by malware at least once in 2013-2014. In 60% of the registered attacks the malware used had a “financial” nature. While there’s seemingly nothing unexpected a certain twist is present…

A critical civilian system goes down – it’s a scenario that evokes some apocalyptic pictures of destruction and mayhem; remember, for instance, “Die Hard 4.0”? Actually this could happen with any corporate infrastructure, since all of them have certain critical systems of their own.

Linux bugs may affect or directly threaten entire virtualization infrastructures: Whatever OS is used on VMs, an attack on a hypervisor is possible from both the outside and inside, and exploitation of the dreaded Shellshock vulnerability on Linux-based hypervisors is a possibility, too.

A data access policy becomes an issue for any company as soon as it accumulates a considerable amount of valuable and sensitive data. That doesn’t mean the policy is always in place when it should be, or that it’s implemented properly.
Can a business be “partially” prepared to ward off cyberthreats? That’s up for debate, but it seems there is little difference between “partial protection” and no protection at all.

The recent developments with “big bugs” such as Heartbleed and Shellshock created a global security strain, with many questions emerging. Both bugs were open-source software-related, but indirectly they would constitute a threat to Windows-based infrastructure. In this post we review a few scenarios of an attack on mostly Windows-based network with Linux servers at certain points.

APT is a term often mentioned in cybersecurity bulletins. Here’s what you need to know to understand it.

IT workers routinely set up limited privileges for all users for security sake. However, the users are extremely suspicious about these sorts of limitations, assuming (sometimes reasonably) that it will affect the workflow. Is there a way to mitigate these contradictions?

Interpol just released an alert regarding cyber-attacks targeting multiple ATMs around the world. During the course of a forensic investigation performed by Kaspersky Lab, researchers discovered a piece of malware infecting ATMs that allowed attackers to empty the cash machines via direct manipulation, stealing millions of dollars.

2014 is making its way into Cybersecurity history books with two global-scale software bugs discovered over 6 months. They are obviously not the last ones, and it is actually a good thing.

Kaspersky Lab launches its solution Kaspersky DDoS Protection in Europe. A distributed network of data cleaning centers vs. distributed attacks.

Kaspersky Lab has signed a cooperation agreement with INTERPOL and a memorandum of understanding with Europol to extend the scope of collaboration between the company and the law enforcement agencies in their joint fight against cybercrime.

We’ve gathered information for patching the most common Linux distros against the notorious Shellshock Bash Bug. If you see we’ve missed something, please drop us a tip!

It’s been a day since the BashBug aka Shellshock bug was disclosed. What real damage has been inflicted and who is most in danger?

A new nasty bug discovered in Bourne again shell set the infosec on fire, Heartbleed-style. Is it as dangerous as the notorious OpenSSL flaw? It depends…

iOS-based devices have a large share in the enterprise, which assures a strong demand for BYOD-oriented security features. A number of them arrive in iOS 8.

The healthcare and financial services industries are among those especially reluctant to implement newer technologies, security included, and believe they have a good reason for that.