
Can we beat software vulnerabilities?
Can we beat software vulnerabilities? It is not possible to do so completely, but there are ways to mend the issue.
3961 articles

Can we beat software vulnerabilities? It is not possible to do so completely, but there are ways to mend the issue.

We recently approached our experts and asked which books they would recommend for would-be malware analysts. Here is their list.

Internet scammers are quite smart and greedy, and know how to disguise their traps, but there are always some ways to find out where these traps are.
Community Health Systems breach exposes the Social Security numbers of 4.5 million patients. Were you a victim? If so, how do you react?
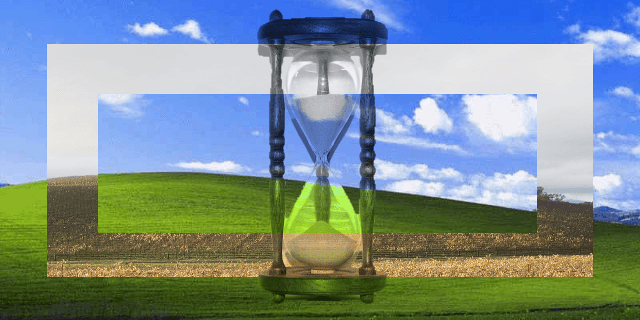
Windows XP’s longevity is fascinating – and terrifying from the security point of view. The latest survey shows it’s still around – over 16% of KSN users still use Windows XP, but it is also clear that its epoch is near the end.
A recent survey shows that IT professionals have a very uneven understanding of how to protect their virtualization environments. Baseline awareness exists, but there’s a Roman Colosseum of room for improvement.

We have bought our very own Blackphone to check its security firsthand.

The new version of Kaspersky Internet Security has performance improvements from 10 to 1000 percent in various scenarios. Good reason to try it!

High-tech crime sounds impressive, but actually the tools are the only somewhat high-tech part, the goals almost never are.

In this short video, we will explain six steps you can take to conveniently maximize the security of your PayPal account.

A recap of last week’s security news and research from the Black Hat hacker conference in Las Vegas, Nevada.
Unpatched flaws in Android make your device vulnerable to “Invisible” infection. You better find out now in order to protect yourself.

Malware using Tor for communication with C&C servers is a novelty; it may not make the malware itself more dangerous, but eradicating it becomes a much more serious problem.

Some things we routinely do in the office are dangerous for careers as they pose significant risk to the company’s business. It’s equally relevant for CEO and intern alike, so watch out!
According to a recent Kaspersky Lab and B2B International survey, 21% manufacturing businesses lost their intellectual property to security breaches. In most cases malware was the cause, although other problems were named.

No one likes support helpline queues, and we have some tools to provide you with an answer to your question almost instantly.

Four years after the discovery of the Stuxnet worm, the primary vulnerability it had been exploiting is still around. This is mainly the problem of poorly maintained Windows XP PCs and servers, most likely inhabited by worms. In the interconnected world a neglected PC or a server is a possible problem for many people.

Losing your work or personal data is a computing worst case scenario. While there is no shortage of ways you can lose your data, there are also a number of protections that can help.

Is social engineering beatable? Just as much as you can beat any other kind of deceit. Actually, social engineering is about “exploiting flaws in a human hardware”.

Yahoo plans to implement end-to-end encryption for all of its mail users, giving normal, non-technical users the power to communicate securely and privately.